Are you confident your network firewall is doing everything it can to protect your data? A strong firewall isn’t just a switch you turn on—it’s a carefully managed shield that guards your business from threats lurking online.
If you want to stop hackers before they even get close, you need to know the best ways to set up and manage your firewall. This guide will walk you through simple, effective steps to keep your network safe and secure.
Keep reading to learn how to make your firewall work smarter—not harder—for you.
Choosing The Right Firewall
Choosing the right firewall is important for network security. It protects your data from unauthorized access and threats.
There are many types of firewalls. Each has its own strengths and fits different needs.
Types Of Firewalls
Firewalls come in several types. Some focus on filtering traffic, while others offer more control and features.
- Packet-Filtering Firewalls: Check data packets for allowed addresses.
- Stateful Inspection Firewalls: Track active connections for better security.
- Proxy Firewalls: Act as middlemen to filter requests.
- Next-Generation Firewalls: Combine multiple security features.
Hardware Vs Software
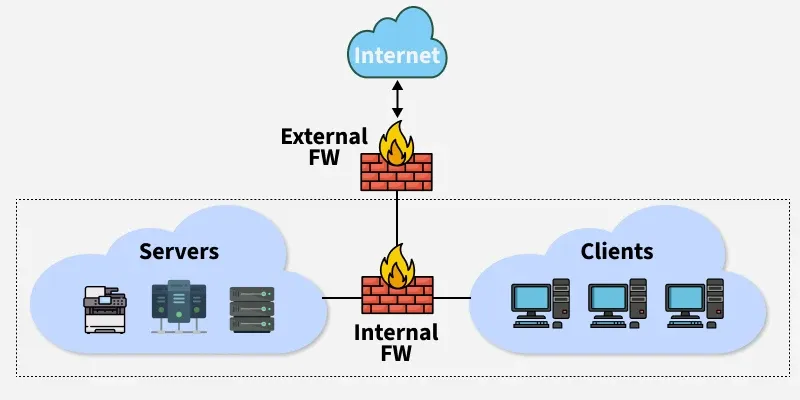
Hardware firewalls are physical devices that protect your network. They are placed between your network and the internet.
Software firewalls run on individual computers. They monitor and control network traffic for that device.
- Hardware Firewalls:
- Protect entire networks
- Good for businesses
- Software Firewalls:
- Protect single devices
- Easy to install and update
Cloud-based Options
Cloud-based firewalls work in the cloud instead of on your premises. They filter traffic before it reaches your network.
These firewalls are flexible and scale easily. They can protect users and devices anywhere.
- No need for physical hardware
- Easy to manage and update
- Good for remote work setups
- Can integrate with other cloud services
Configuring Firewall Rules
Firewall rules control the flow of network traffic. They help protect your network from threats.
Setting up rules correctly ensures only safe data moves in and out of your network.
Allow Vs Deny Rules
Allow rules let specific traffic pass through the firewall. Deny rules block unwanted traffic.
Use allow rules to permit trusted connections. Use deny rules to stop harmful or unknown sources.
- Allow rules open ports or services for trusted users
- Deny rules block dangerous or suspicious activity
- Always start with deny all and allow only needed traffic
- Review rules regularly to keep security tight
Managing Inbound And Outbound Traffic
Inbound traffic comes from outside your network. Outbound traffic goes from inside to outside.
Control inbound traffic to stop attacks. Manage outbound traffic to prevent data leaks.
- Inbound rules block harmful external access
- Outbound rules limit which apps can send data out
- Log traffic to detect unusual activity
- Use strict rules on both inbound and outbound paths
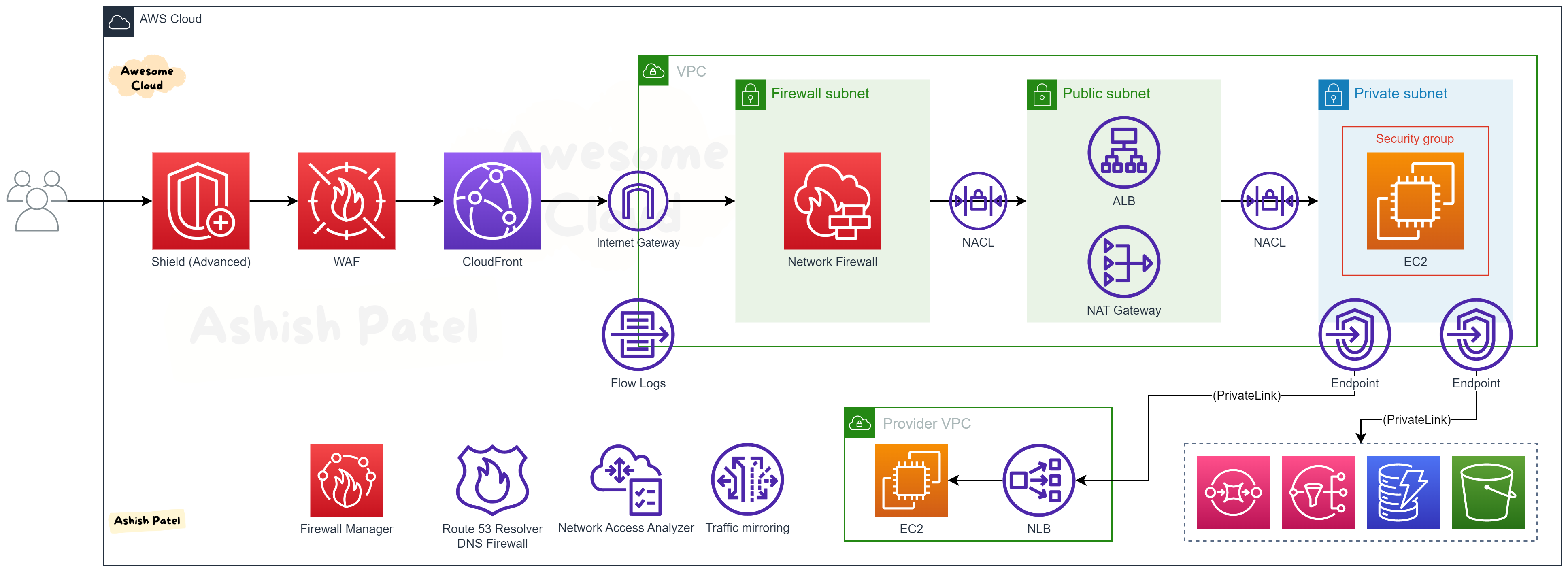
Setting Up Network Zones
Network zones divide your network into parts with different trust levels. Each zone has its own rules.
Zones help control traffic between internal devices, servers, and the internet.
- Public zone for internet-facing servers
- Private zone for internal user devices
- DMZ zone for services needing limited access
- Set rules to limit traffic between zones
Implementing Access Controls
Access controls help protect your network firewall from unauthorized use. They limit who can enter and what they can do.
Good access controls reduce risks and keep your network safe from attacks.
User Authentication
User authentication checks if a person is who they say they are. It stops outsiders from accessing the network.
Strong passwords and multi-factor authentication make user authentication more secure.
- Use passwords with letters, numbers, and symbols
- Enable two-factor authentication for extra safety
- Regularly update authentication methods
Role-based Access
Role-based access gives users permissions based on their job roles. This keeps users from accessing data they do not need.
Limit access to sensitive parts of the network by assigning roles carefully.
- Define clear roles for employees
- Assign minimum permissions needed for tasks
- Review roles and permissions regularly
Vpn Integration
VPNs create a secure connection for remote users. They protect data as it travels over the internet.
Integrate VPNs with your firewall to control who can access the network remotely.
- Use VPNs to encrypt remote connections
- Set firewall rules to allow only VPN traffic
- Monitor VPN access for unusual activity
Regular Updates And Patch Management
Network firewalls protect your systems from threats. Keeping them updated is key to strong security.
Regular updates fix bugs and close security gaps. Patch management helps keep firewalls reliable.
Firmware Updates
Firmware is the software inside your firewall hardware. Updating firmware improves performance and security.
New firmware versions fix errors and add new features. Install updates as soon as they become available.
Security Patch Schedules
Set a regular schedule to check for security patches. This helps avoid missing important fixes.
Plan patching during low-traffic hours. This reduces downtime and impact on users.
- Check vendor sites weekly for new patches
- Test patches in a safe environment first
- Apply patches quickly after testing
- Keep records of all patch activities
Automating Updates
Automation saves time by installing updates automatically. It reduces human errors and delays.
Use built-in firewall tools or third-party software. Configure automation to notify you after updates.
- Enable auto-update features in firewall settings
- Set alerts for update successes or failures
- Regularly review automated update logs
- Keep backups before running updates automatically
Monitoring And Logging
Network firewalls protect your system from unwanted traffic. Monitoring and logging help you keep track of this traffic.
These practices let you detect threats early and fix problems fast. They also help improve your firewall’s performance.
Traffic Analysis
Traffic analysis means watching data that passes through your firewall. It shows what kind of traffic is normal or suspicious.
Look for unusual spikes or unknown sources. This helps you find attacks or errors in your system.
- Track inbound and outbound connections
- Identify blocked and allowed traffic
- Watch for unexpected data flows
- Analyze traffic patterns regularly
Alert Configuration
Set up alerts to notify you about important events. Alerts help you act fast on security issues.
Choose alert types that match your network risks. Avoid too many alerts to reduce noise.
- Alert on blocked intrusion attempts
- Notify on policy violations
- Set thresholds for traffic spikes
- Use email or SMS for critical alerts
Log Review Best Practices
Regular log reviews help you find threats and fix errors. Logs record all firewall activity and decisions.
Keep logs organized and easy to search. Use tools to automate log analysis and spotting issues.
- Store logs securely for a set time
- Check logs daily or weekly
- Look for repeated failed access attempts
- Use log management software
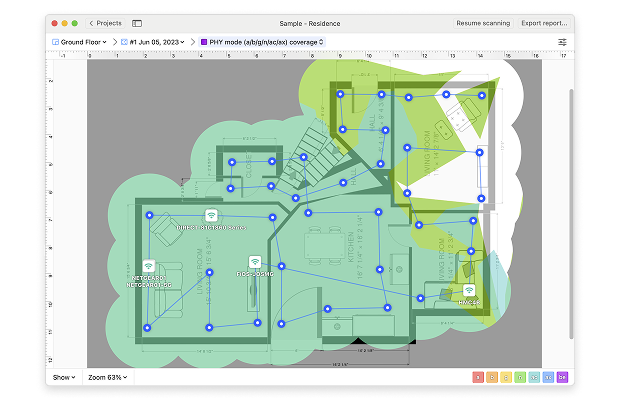
Credit: medium.com
Advanced Security Features
Network firewalls protect computers from harmful traffic. Advanced features help stop new and hidden threats.
These tools look deeper into data and watch for bad activity. This makes networks safer and stronger.
Intrusion Detection Systems
Intrusion Detection Systems (IDS) watch network traffic for signs of attacks. They alert admins about suspicious actions.
IDS can spot unusual patterns that show hacking attempts or malware infections early on.
- Monitor network traffic continuously
- Detect known attack signatures
- Alert administrators in real time
- Help prevent data breaches
Deep Packet Inspection
Deep Packet Inspection (DPI) looks inside data packets. It checks content beyond basic headers for threats.
DPI can find hidden malware or unsafe files before they reach the user’s device.
- Examines packet payloads thoroughly
- Blocks harmful content at the network edge
- Improves firewall accuracy and security
- Supports compliance with security rules
Application Layer Filtering
Application Layer Filtering controls which apps can send or receive data. It blocks unwanted or risky applications.
This filtering stops attacks that use apps to hide malicious actions or steal data.
- Filters traffic by application type
- Blocks unauthorized app usage
- Prevents data leaks through apps
- Improves overall network control
Backup And Recovery Plans
Network firewalls protect your data and systems from threats. Having a backup and recovery plan ensures your firewall stays effective.
These plans help you restore your firewall quickly after a failure or attack. This keeps your network safe and running.
Firewall Configuration Backup
Backing up your firewall settings saves the exact rules and policies you use. This backup helps you restore configurations fast if needed.
Store backups in a secure, separate location. Update backups regularly to capture all recent changes.
- Save configuration files after every change
- Use automated tools to schedule backups
- Keep backups in encrypted storage
- Maintain multiple backup copies
Disaster Recovery Strategies
Create clear plans to restore firewall services after disasters. These plans reduce downtime and data loss.
Include steps to recover hardware, software, and settings. Assign roles and responsibilities to your team.
- Identify critical firewall components
- Plan for hardware replacement or repair
- Prepare for software reinstallation
- Document recovery procedures clearly
- Train staff on their recovery tasks
Testing Recovery Procedures
Test your recovery plans regularly to make sure they work. Testing finds problems before a real disaster happens.
Run simulations of failures and recoveries. Check if backups restore correctly and if team members follow steps well.
- Schedule regular recovery drills
- Verify backup data integrity
- Review and update recovery documents
- Train new staff on recovery steps
- Improve plans based on test results
Credit: www.geeksforgeeks.org
Training And Awareness
Network firewalls protect important data from threats. People must know how to use them well.
Training helps staff understand risks and follow security rules. Awareness keeps systems safer every day.
Staff Training Programs
Train all employees on firewall basics and security policies. This helps reduce mistakes that cause breaches.
Use clear lessons and simple examples to explain firewall rules. Repeat training regularly to keep skills fresh.
- Explain firewall purpose and function
- Show how to identify security risks
- Practice safe internet and email use
- Review company security policies
- Test knowledge with quizzes or drills
Phishing And Social Engineering
Phishing tricks users into giving away passwords or access. Staff must learn to spot fake emails and links.
Teach employees to verify requests and never share login info. Awareness reduces chances of firewall breaches.
- Look for suspicious email senders
- Check links before clicking
- Do not open unknown attachments
- Report strange messages to IT
- Use strong, unique passwords
Regular Security Audits
Audits check if firewalls and rules work well. They find weak spots before attackers do.
Schedule audits often and fix problems quickly. Training staff to help with audits improves security overall.
- Review firewall rule settings
- Test firewall responses to threats
- Check for unauthorized changes
- Update firewall software and hardware
- Train staff on audit findings and actions

Credit: www.esecurityplanet.com
Frequently Asked Questions
What Is A Network Firewall?
A network firewall is a security device that monitors and controls incoming and outgoing network traffic. It establishes a barrier between a trusted internal network and untrusted external networks, such as the internet. Firewalls can be hardware, software, or a combination of both, and they are crucial for network security.
How Does A Firewall Protect Your Network?
Firewalls protect networks by filtering traffic based on predefined security rules. They block unauthorized access while permitting legitimate traffic. Firewalls can prevent cyberattacks by monitoring traffic and identifying malicious activity. They also help protect sensitive data from being accessed by hackers or unauthorized users.
What Are Common Firewall Configuration Mistakes?
Common mistakes include using default settings, not updating firmware, and misconfiguring rules. Failing to regularly review and update firewall rules can create security gaps. Over-permissive rules and lack of segmentation can lead to vulnerabilities. Regular audits and updates are essential for maintaining firewall effectiveness.
Why Is Firewall Logging Important?
Firewall logging is crucial for monitoring network activity and identifying security incidents. Logs provide insights into traffic patterns and can reveal unauthorized access attempts. They help in forensic analysis and compliance reporting. Reviewing logs regularly can help detect potential threats and improve network security.
Conclusion
Strong network firewalls protect your data and devices daily. Keep rules clear and updated to block threats fast. Monitor traffic often to spot unusual activity early. Use simple settings that suit your network size and needs. Train your team to follow firewall policies strictly.
Regular checks help fix weak spots before attacks happen. Good firewall habits make your network safer and stronger. Stay alert, stay secure.
19 min read